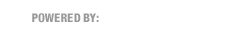
We have ourselves a doozy today. Several of our CASE staff received this one. Take a look:
This email was actually pretty sophisticated for a few reasons:
- It was probably sent by a piece of malware called a Worm. Worms self-perpetuate by hijacking people’s email accounts and sending messages to everybody in their contact lists.
- Therefore, it was probably actually sent from a real email account at UCP Greater Chicago (the people behind Infinitec). Note that Peggy Zegley is a real person and the signature area of the email contains correct information.
However, there are some red flags that savvy people will recognize:
- The absence of a personal greeting mentioning the recipient by name.
- The poor English.
Note that you can’t always count on these red flags, as phishing attacks are becoming more and more sophisticated, but if you see them, beware.
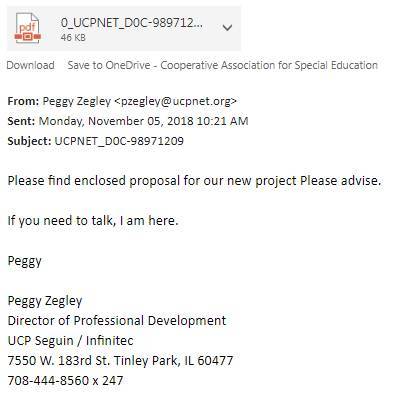
I opened the attached PDF as a preview in Outlook and got this:
OK so encrypted documents is a real thing, but typically only from hospitals and organizations sending sensitive student data; not something like this. Also nobody sends PDFs with buttons in them.
If you highlight (don’t click) the button, you’ll see an address that clearly has nothing to do with Adobe Document Cloud:

saldejums.ee? What the heck is that?
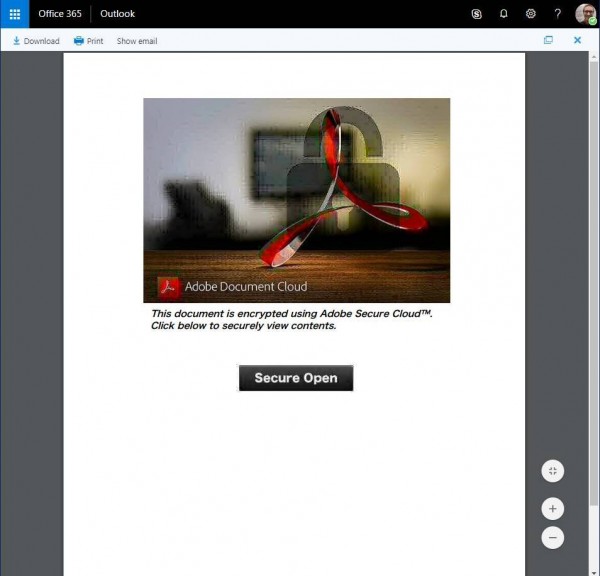
So on a test computer, I visited the link to see what’s up. Turns out it shows a very persuasive Office 365 login page. All it would take is an innocent log in and the bad guys would have your Office 365 password.
How persuasive? Check out this comparison between a real Office 365 login (left) and the fake (right).
The fake is well-done. It’s not obvious without seeing them side-by-side. Some clues:
- The address was still that weird “saldejums.ee” thing. A real Microsoft login address contains: “login.microsoftonline.com”
- The links do not work, including “Create one!” and “Terms of use” and “Privacy & Cookies”–they just return you to the fake login screen.
So there you go. Keep an eye out for stuff like this, and keep sending me your suspicious emails!